The Onion Routing (TOR) is a decentralized network designed to keep your identity private and your activity anonymous online. By routing your traffic through multiple volunteer-operated relays and layering encryption—like the layers of an onion—TOR makes it extremely difficult for anyone to trace your browsing back to you.
What Is Onion Routing?
Onion routing wraps your data in several layers of encryption. As the traffic passes through each relay (also called a node), one layer is peeled away to reveal only the next destination. No single relay knows both who you are and where you’re going, which provides strong anonymity for users.
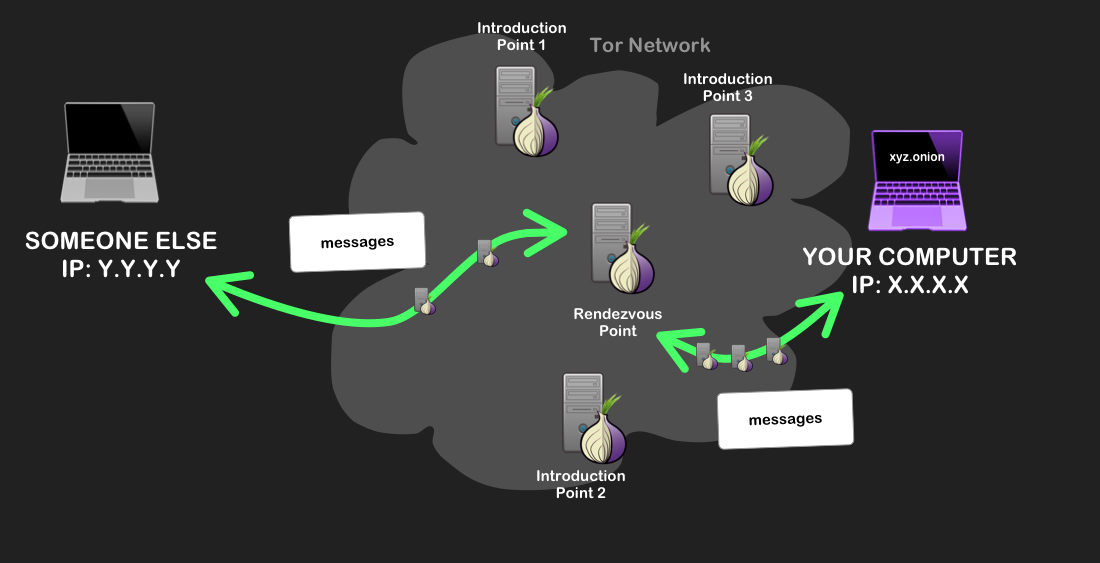
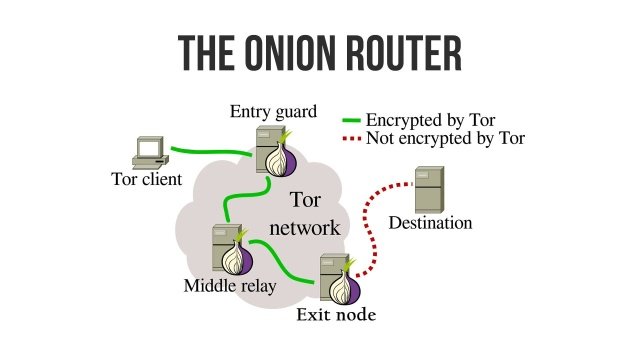
How the TOR Network Works
1. Entry (Guard) Node
Your device first connects to a guard node. It knows your IP address but can’t see your final destination because the payload remains encrypted.
2. Middle Relay
The traffic is passed through one or more middle relays. These hop your data across the network without revealing source or destination.
3. Exit Node
The final relay—called the exit node—decrypts the last layer and sends the request to the target website. It can see the destination but not the original sender.
Benefits of Using TOR
Privacy & Anonymity
By splitting knowledge across different relays, TOR prevents ISPs, advertisers, and surveillance actors from building a complete profile of your activity.
Censorship Resistance
TOR helps users bypass geographic blocks and state-level censorship, supporting journalists, activists, and citizens in restrictive environments.
Access to .onion Services
TOR enables access to hidden services (websites with .onion domains) that are not indexed by conventional search engines.
Limitations You Should Know
Speed Trade-offs
Because your traffic hops through multiple relays, browsing can be slower than using a direct connection.
Exit Node Risks
Unencrypted traffic leaving an exit node can be observed. Always use HTTPS sites and avoid sharing personal data.
Operational Security (OpSec)
TOR hides your network path, not your behavior. Logging into personal accounts, installing risky extensions, or revealing identity details can still expose you.
Getting Started With TOR
Use the TOR Browser
Download the official TOR Browser, keep it updated, avoid additional plugins, and use HTTPS wherever possible.
Combine With Good Practices
Disable unnecessary scripts, be cautious with downloads, and consider a reputable VPN if your local network blocks TOR (use in the correct order and understand the trade-offs).
Bottom Line
TOR remains a powerful tool for privacy, anonymity, and censorship resistance. While it isn’t a silver bullet, careful usage—with attention to HTTPS, OpSec, and trusted software—can meaningfully protect your online identity.
The Role of Technology in Environmental Conservation and Monitoring
Website design and development firm
![]()